Summary
This document will guide you through the steps to enable multi-factor authentication and Single-Sign On for Weekdone (https://weekdone.com/).
System Requirements
- PhenixID Authentication Server 2.0 or higher
- Weekdone administration rights
- The users to be federated must be present in Weekdone (Manually added or automatically provisioned)
Instruction
Overview
This document will guide you through the steps to enable multi-factor authentication and Single-Sign on for Weekdone.
PhenixID Server acting as SAML IdP
- Setup PhenixID Authentication Services as a SAML IdP using one of the Federation scenarios described here. (If the desired authentication method is not provided by a scenario, use the documentation for the SAML authenticator here)
- Depending on your setup, fetch the Weekdone userID value from the appropriate attribute (typically sAMAccountName (or uid if using other LDAP directory)) on the user object.
- Use sAMAccountName/uid as Name ID attribute.
- Go to Scenarios->Federation-> <newly_added_scenario> -> Identity Provider. Deselect “Require signed requests”. Save.
- Then export your SAML IdP metadata by going to the URL:
https://<YourServerDomainName>/saml/authenticate/<authenticator_alias>?getIDPMeta
and download the metadata to a xml file. - Save the IDP Signing Certificate as a file (follow this instruction)
- Fetch the SingleSignOnService -> Location value.
- Fetch the SingleLogoutService -> Location value.
Configure Weekdone
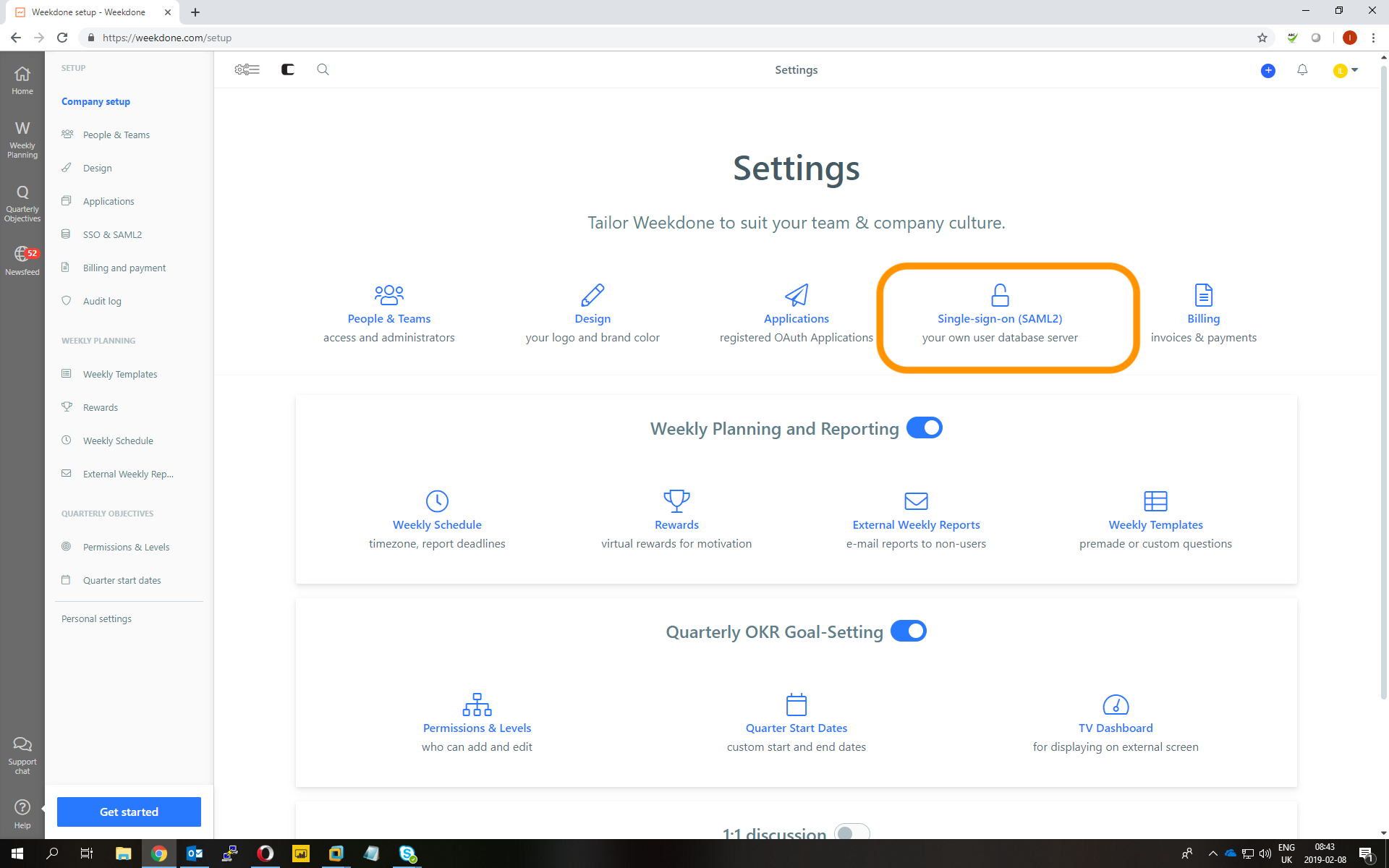
- Login to Weekdone as a Weekdone admin (for your domain)
- Navigate to company settings
- Click Single-Sign-On (SAML2)
- Change these settings:
– SAML name. Set this to your company name, for example company.
– SAML SSO URL. Set this to the SingleSignOnService -> Location value of the IdP, fetched in previous step above.
– SAML Logout URL. Set this to the SingleLogoutService -> Location value of the IdP, fetched in previous step above.
– X599 Certificate. Cut this out from the IDP Signing Certificate file created in previous step above. Make sure PEM header and footer (—–BEGIN.. and —–END… is not included).Example:
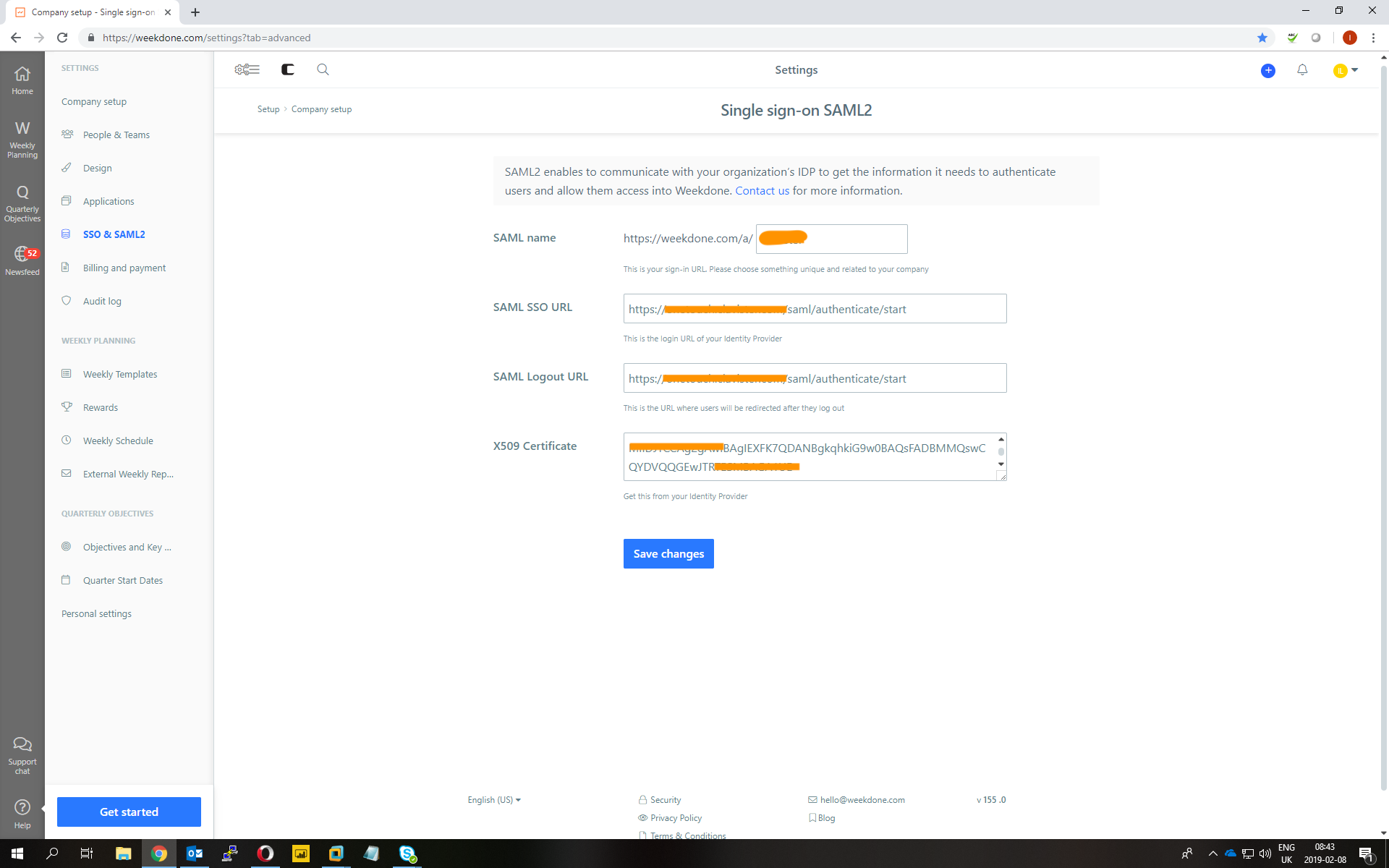
- Click Save changes
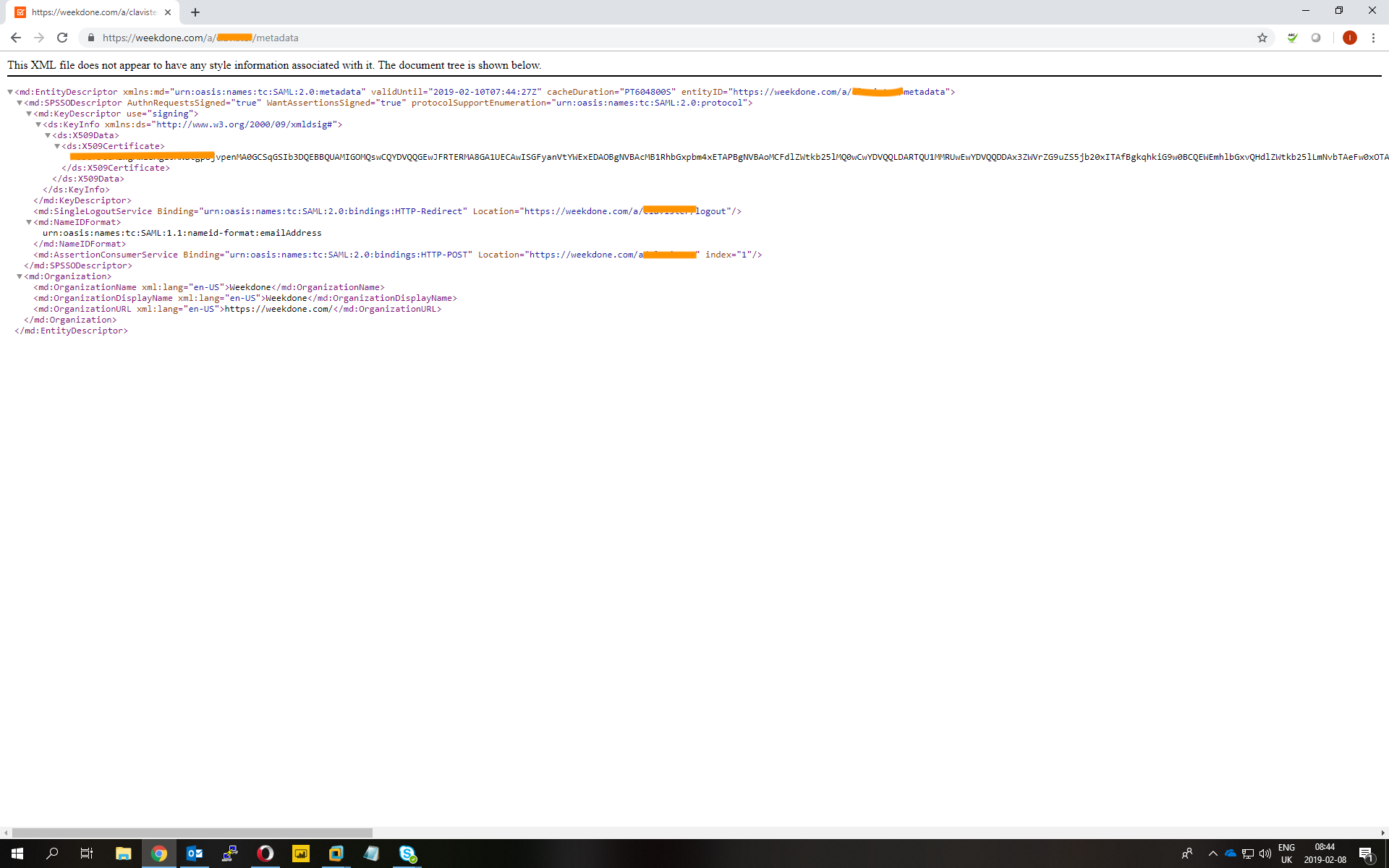
- Open a new web browser tab and go to https://weekdone.com/a/<your_saml_name>/metadata
Example: https://weekdone.com/a/company/metadata - SAML Metadata for your weekdone domain should now be presented.
Example:
Add trust to Weekdone on PhenixID Authentication Services
- Login to configuration manager
- Open Scenarios->Federation->SAML Metadata upload
- Click the plus sign
- Add Weekdone SAML SP Metadata by entering the Weekdone metadata url. (Example: https://weekdone.com/a/company/metadata)
Test
- Browse to your Weekdone site (Example: https://weekdone.com/a/company)
- This should result in a redirect to PhenixID Authentication Server
- Authenticate
- If authentication was successful, a redirect to Weekdone should occur (with SAML assertion)
- The user should now be logged in.
DISCLAIMER
Information provided in this document is for your information only. PhenixID makes no explicit or implied claims to the validity of this information. Any trademarks referenced in this document are the property of their respective owners.The origin of this information may be internal or external to PhenixID. PhenixID makes all reasonable efforts to verify this information.
PhenixID - support.phenixid.se