Release of IM 5.4.1
April 28th 2020
PhenixID Identity Manager 5.4.1 improves the stability, compatibility and security of your solution, and is recommended for all installations.
1. Update of bundled Apache Tomcat
We always try to stay in synch with current Tomcat releases. Since the Ghost Cat bug was discovered we have updated Tomcat to 8.5.53 for this release. Ghost Cat bug had to do with vulnerability using the AJP connector, IM can in some scenarios use AJP with Microsoft IIS.
For more information about Ghost Cat bug, please read TrendMicroBloggGhostCat
We have also updated our recommendations regarding the use of AJP with IIS. If you are using AJP and are upgrading to IM 5.4.1 you need to read PSD1079 for configuration changes.
For more information about AJP with IIS, please read PSD1079
If you are unable to update Identity Manager to this version right away or if you are upgrading to IM 5.4.1 and you are NOT using AJP, then disable the AJP protocol.
Open server.xml in \..\PhenixID\IM\server\conf and find line
<Connector port=”8009″ protocol=”AJP/1.3″ redirectPort=”8443″/>
Change the line to disable AJP like shown below:
<!– <Connector port=”8009″ protocol=”AJP/1.3″ redirectPort=”8443″/> –>
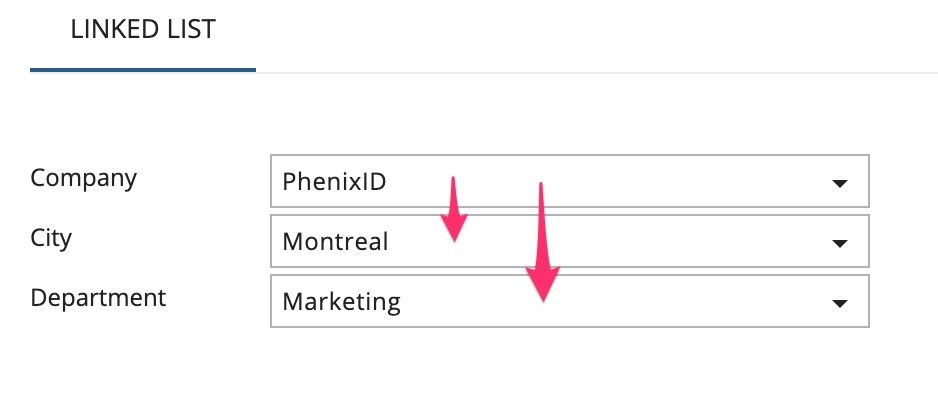
2. Linked list custom control
A new custom control is created to support drop down lists to integrate with each other.
Use case: You have a drop down list where you for example can select different companies. If you select for example company PhenixID then that value is sent to other drop down lists and trigger what to display in those underlying lists.
For more information, please read PSD1147
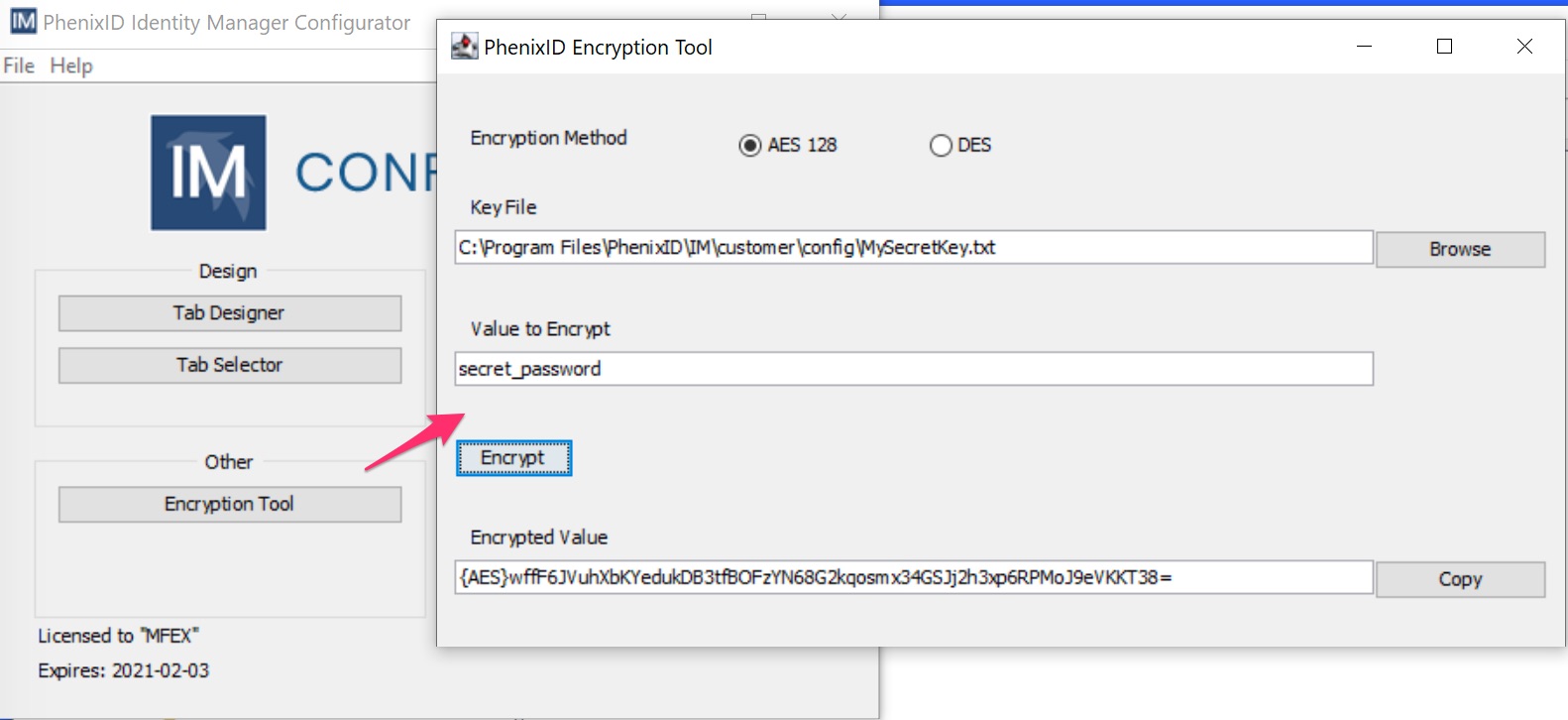
3. Support for AES encryption
Different type of data needs to be encrypted, for example the password for the IM service account. If you like to encrypt the password, or any other data, you can now use AES-128 to do this.
For more information, please read PSD1142
4. Error when “Save and Close” correction
If you change an object and click “Save and Close” and this change means that no valid form can be associated with the changed user, you get an error stating “Insufficient access rights to this object!” at the bottom of the screen.
This has now been corrected.
5. Clarification of MyDN, ThisDN, LDAP(attribute)
We have received some requests of adding support for logged in user, user currently being edited, user attribute of logged in user for example.
Especially using information of the logged in user in tab restrictions or predefined search have been requested.
For more information this, please read PSD1145
6. SAML authentication filter improvements
- When LOGOFFURI policy is configure and used, the query string status=3&target=/im/NEIDMgmt should not be added by default when logoff. This has been corrected.
- All unauthenticated requests will now be redirected to the configured SAML IdP.
- If there is no match on the authentication attribute, IM redirected to the application login page. This is not suitable in a SAML scenario. The behavior has now been corrected.
7. AAMEditFilter and MultiListStingControl correction
AAMEditFilter did not handle MultiListStringControl values.
This has been corrected, the fix also include MultiListControl and MultiListStaticStringControl.
8. New filter to find and replace characters in a string
If you like to find a word or a single character and replace it with another word or character, please read PSD1144
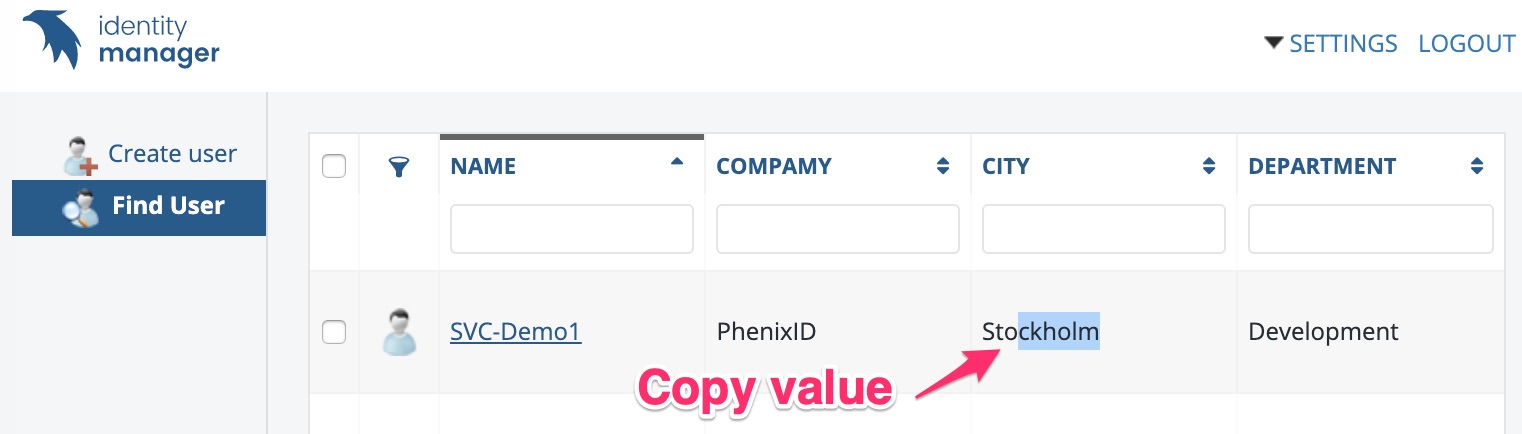
9. Copy value in result set
This is a feature that was removed some time ago. We have now reintroduced that feature again.
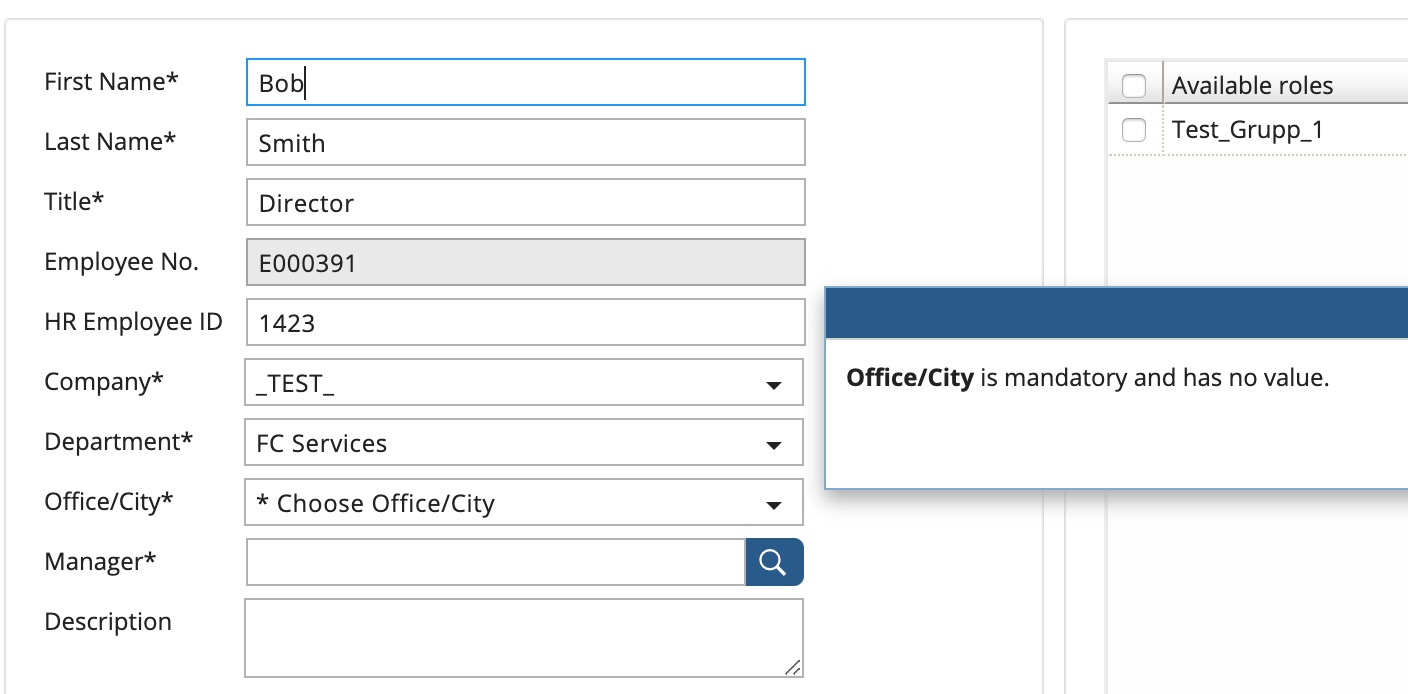
10. Custom mandatory popups
If you have a create or an edit form and have some control as mandatory IM includes a mandatory parameter for that. This control have however a standard popup which links to the attribute which can in some cases be misleading for the user.
We have created a filter to be used instead of the mandatory checkbox which you can use to create your own custom popups.
For more information this, please read PSD1150
11. Update to log4j2.xml
The log4j2.xml file is updated to cover more log-events. Since an upgrade does not cover the /customer folder you need to update this manually. If you do a clean installation you do not have to do anything.
If you need to update the current log4j2.xml file:
- If you have not changed anything in log4j2.xml since you installed your current version, then you can simply do a clean installation (in a temp folder) and copy the new file and replace it with the one in your installation.
- If you can not replace, then the line to update is:
Find following line in your current log4j2.xml
<Logger name=”im.se.nordicedge” additivity=”false” level=”info”>
replace that line with
<Logger name=”im” additivity=”false” level=”info”> - Changed default pattern for audit logging
The change below is not mandatory. Just FYI. It will dictate the format in audit.log.
Find following line in your current log4j2.xml
[EVENT] %-5level %d{MMM dd yyyy HH:mm:ss.SSS/zzz} %msg%n
replace that line with
%d{yyyy-MM-dd’T’HH:mm:ssXXX} %m%n
12. IM Configurator updates
AES/DES tool added
Tool is added to generate AES and DES encrypted data.