Summary
This document will guide you through the steps to provide Single-Sign-On to G Suite using SAML with PhenixID Authentication Services as SAML IdP.
System Requirements
- PhenixID Authentication Services 2.0 or higher
- Google domain registered (for example example.org)
- Google domain administrator account credentials
- Google test account (must NOT have administrator rights)
Instruction
1. Set up PhenixID Authentication Services as SAML IdP
- Setup PhenixID Authentication Services as a SAML IdP using one of the Federation scenarios described here. (If the desired authentication method is not provided by a scenario, use the documentation for the SAML authenticator here)
Make sure the User identifier attribute is set to the attribute where the mail address is stored. - Download the IdP signing certificate to a file as described here.
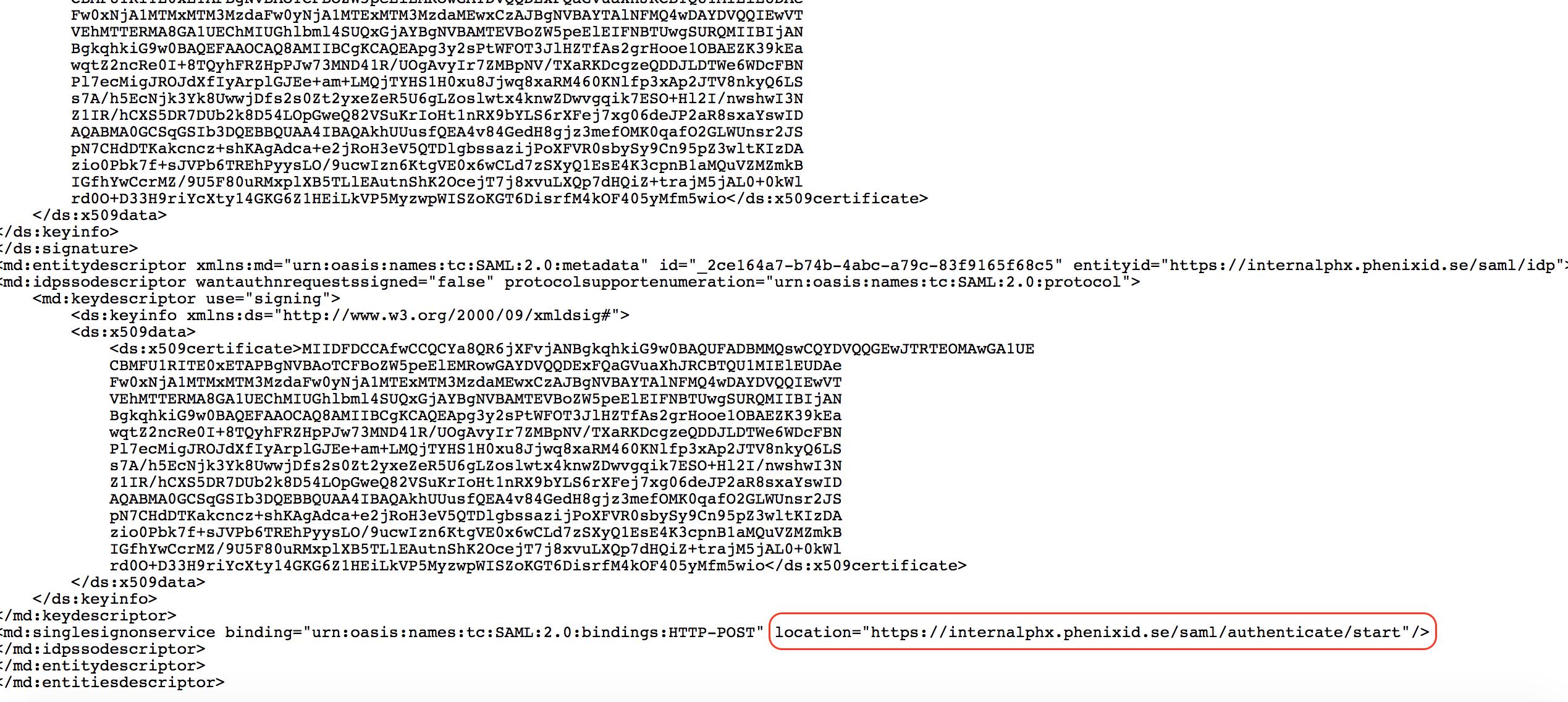
- Open the IdP Metadata and get the value of the SingleSignOnService-Location.
- If SAML SLO is configured (http://document.phenixid.net/m/69842/l/751485-saml-configure-single-logout-slo), get the SLO Post URL.
2. Configure G Suite
-
- Login to https://admin.google.com with yoyr G suite administrator account.
- Click Security in the admin console.
- Click Setup Single Sign on
- Select Setup SSO with third party identity provider.
- Enter these properties:
- Sign-in page URL = <Value fetched from step 1.3>
- Sign-out page URL = <Value fetched from step 1.4>
- Verification certificate = <Upload certificate file from step 1.2>
- Select “Use a domain specific issuer”
- Example configuration:
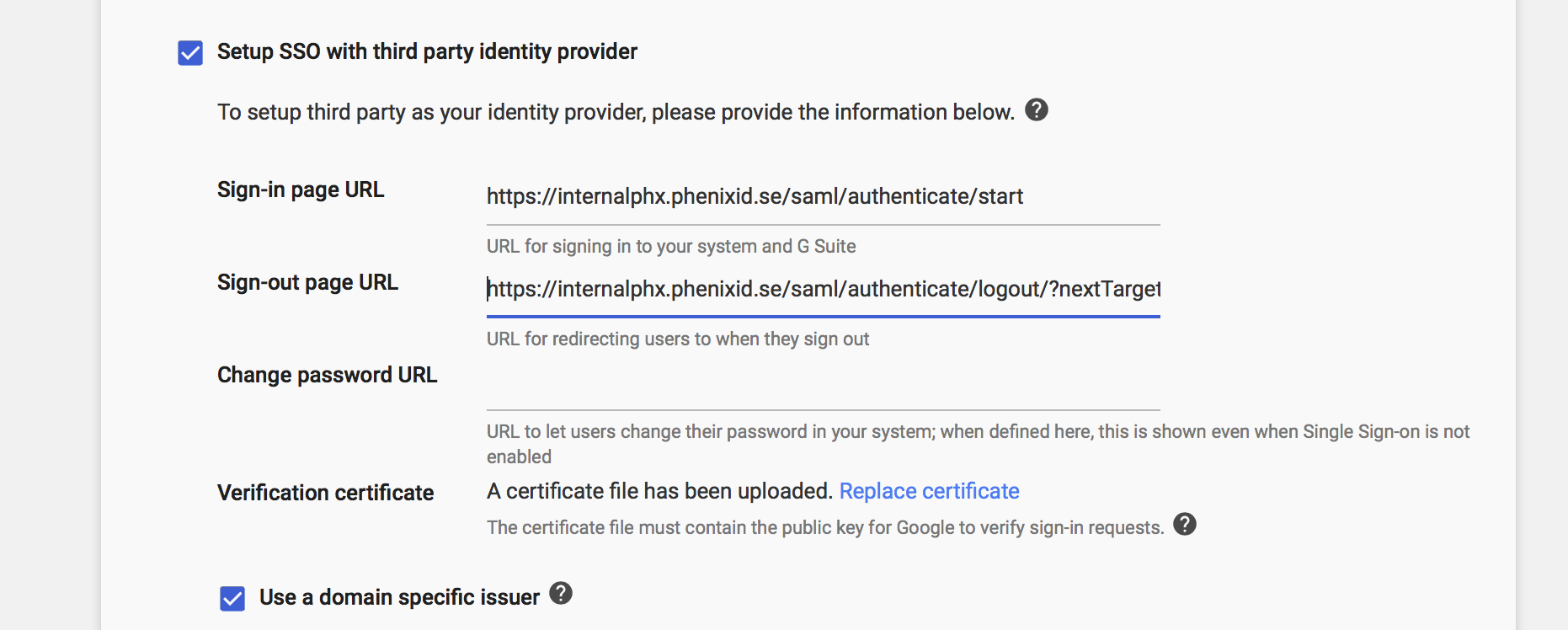
- Click Save
3. Add G Suite SAML SP Metadata to PhenixID Authentication Services
- Create GSuite SAML SP Metadata XML file. Use the template data below and replace “<your_domain>” in entityID and AssertionConsumerService Location with your google domain name. Place the text in a file using a text editor and save it as a xml file.
<?xml version="1.0" encoding="UTF-8"?> <EntityDescriptor entityID="google.com/a/<your_domain>" xmlns="urn:oasis:names:tc:SAML:2.0:metadata"> <SPSSODescriptor protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol"> <NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified</NameIDFormat> <AssertionConsumerService index="1" Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://www.google.com/a/<your_domain>/acs"></AssertionConsumerService> </SPSSODescriptor> </EntityDescriptor>
- Example metadata:
<?xml version="1.0" encoding="UTF-8"?> <EntityDescriptor entityID="google.com/a/glab.thebjorks.se" xmlns="urn:oasis:names:tc:SAML:2.0:metadata"> <SPSSODescriptor protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol"> <NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified</NameIDFormat> <AssertionConsumerService index="1" Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://www.google.com/a/glab.thebjorks.se/acs"></AssertionConsumerService> </SPSSODescriptor> </EntityDescriptor>
- Example metadata:
- Upload the metadata file using this Federation Scenario.
Test
- Open a web browser
- Browse to https://mail.google.com and enter your emailadress.
OR
Browse to https://mail.google.com/a/<your_domain> - You should be redirected to the Idp (PhenixID Authentication Services)
- Authenticate
- You should be redirected back to G Suite
- You are now logged in to G Suite.
Troubleshooting
Use the SAML Tracer addon for Firefox to debug and trace the SAML messages.
DISCLAIMER
Information provided in this document is for your information only. PhenixID makes no explicit or implied claims to the validity of this information. Any trademarks referenced in this document are the property of their respective owners.The origin of this information may be internal or external to PhenixID. PhenixID makes all reasonable efforts to verify this information.
PhenixID - support.phenixid.se